Jurisdictions
- Bermuda
- Guernsey
- Bahamas
- Barbados
- Seychelles
- Liechtenstein
- Singapore
- British Virgin Islands
- Hong Kong
- Luxembourg
- Antigua
- Switzerland
- Cayman Islands
- Nevis
- New Zealand
- Belize
- Netherlands
- Ireland
- United Kingdom
- United Arab Emirates
- Mauritius
- Jersey
- Labuan
- Rwanda
- Gibraltar
- Marshall Islands
- Samoa
- Panama
- St Vincent & The Grenadines
- Austria
- Madeira
Industry Sectors
- Hedge Funds and Alternative Investments
- Citizenship and Residency
- International Tax Planning
- Islamic Finance
- Fintech
- Insurance/Reinsurance
- Investment Funds
- Trusts And Foundations
- Private Banking
- Wealth Management
- Philanthropy
- Offshore Securities Markets
- Sustainable Finance
- Family Offices
- Arbitration
- Regulation and Policy
- Comment
- Big Debate
- In the Chair
- Global Regulation & Policy
- Features
- Sector Research
- Jurisdictions
- British Virgin Islands
- Cayman Islands
- Belize
- Bahamas
- Guernsey
- Switzerland
- Bermuda
- Barbados
- Singapore
- Hong Kong
- Luxembourg
- Labuan
- Jersey
- United Arab Emirates
- Ireland
- New Zealand
- Netherlands
- Liechtenstein
- Mauritius
- Antigua
- Rwanda
- Austria
- Seychelles
- Anguilla
- Samoa
- Marshall Islands
- Gibraltar
- Nevis
- United Kingdom
- North America
- Canada
- Asia
- Africa
- Latin America
- Australasia
- Europe
- Industry Sectors
- Hedge Funds and Alternative Investments
- Citizenship and Residency
- International Tax Planning
- Islamic Finance
- Fintech
- Insurance/Reinsurance
- Investment Funds
- Trusts And Foundations
- Private Banking
- Wealth Management
- Philanthropy
- Offshore Securities Markets
- Sustainable Finance
- Family Offices
- Arbitration
- Regulation and Policy
01/12/12
From Sector Research
Global Shell Games: A Mystery Shopping Experiment in Know Your Customer Standards

Michael G Findley, Daniel L Nielson and Jason Sharman provide an in depth look at their recent research into Shell Companies and KYC standards highlighting flaws in compliance in some surprising jusisdictions.
Organised crime and the financing of terrorism depend on financial secrecy. Untraceable shell companies are widely regarded as one of the most important means of providing such financial secrecy. Recognising this danger, international organisations and national governments have responded by mandating Know Your Customer (KYC) standards to enable authorities to ‘look through’ shell companies to find the real individuals in control. Yet as important as these KYC rules are, no one has really known how effective these policy measures have been in achieving their aims. While proponents trumpet the need for corporate KYC standards, critics allege that the standards are an expensive failure.
In response to this fundamental uncertainty, we designed an experiment based on impersonating 21 fictitious low- and high-risk customers and soliciting offers for shell companies from thousands of Corporate Service Providers in 182 countries to test whether and how KYC standards are actually applied in practice. Here we provide a brief summary of the design of the global mystery shopping experiment, as well as the some of the main results.
The exercise was based on creating a variety of fictitious customers who exhibited various types and levels of risk, particularly to do with corruption and the financing of terrorism. Using email approaches, we then had researchers impersonating these customers make 7466 requests for shell companies to 3773 providers. The standard email explained the customer was a consultant looking for tax savings, limited liability and confidentiality, and asked how much a company would cost, and, crucially, what identity documents were required. If providers fail to collect KYC documentation on customers forming shell companies, it is very difficult for the authorities to establish the identity of the beneficial owner further down the track, making the company effectively untraceable.
The risk profile of the customer was manipulated in several ways. The baseline approach came from a customer in one of eight small OECD countries with low levels of corruption and terrorist financing. The corruption risk profile instead had the customer come from West Africa or Central Asia, and work in government procurement, features that in combination with the standard shell company solicitation should have constituted an obvious red flag. Similarly, the terrorism financing risk had the customer being a citizen of one of four countries perceived as having a high terrorism risk, and working for an Islamic charity in Saudi Arabia. Other variations included providing more information about international KYC standards, and suggesting various penalties or inducements for breaking these rules.
Having contacted the provider with a request for a shell company, one of five things could happen. Most simply, the provider could decline to reply, either as a product of commercial logic, inattention or risk aversion. Similar reasoning might lie behind the second outcome, when the provider replied to refuse service. Third, the provider could offer to form a company, but insist on certified identification documents for KYC purposes, a response which we coded as compliant with international standards. If the response asked for some identity documents, but did not specify they had to be certified, this was classified in partially compliant. Finally, if the provider offered a company without asking for any identity documents, this was coded as non-compliant.
Given that the project was based on impersonating fictitious characters and pretending to be interested in buying shell companies, it was based on deception. Indeed, this deception gives us confidence that we did receive genuine answers from providers. But deception must be ethically justified. In line with general principles governing such research, deception can only be justified where (1) the costs are low, (2) subjects are not exposed to any physical or emotional pain, (3) there is no other way to do the research, and (4) there are significant benefits resulting from the research.
By randomly matching customers of varying risk profiles with the providers, it is possible to see how different risks influenced providers’ willingness to reply, and to comply with or violate international KYC standards on the beneficial owners of shell companies. Relative to the low-risk baseline profile, high-risk profiles like those from the corruption and terrorist financing email approaches should have decreased the proportion of providers replying and failing to perform KYC checks, while increasing the proportion insisting on certified identity documents. To what extent were these expectations fulfilled, and what evidence is there as to whether or not KYC rules are effective?
Overall, international rules that those forming shell companies must collect proof of customers’ identity are relatively ineffective. Nearly half (48 per cent) of all replies received did not ask for certified identity documentation, and 22 per cent of all replies received did not ask for any identity documents at all to form a shell company.
We explain many of the results below with reference to a ‘Dodgy Shopping Count’, which measures the average number of providers a particular type of customer would have to approach to receive a non-compliant response, ie, be offered a shell company with no need to supply any identity documents. A five per cent non-compliance rate would thus equal a Dodgy Shopping Count of 20. The lower the Dodgy Shopping Count, the easier it is to get an anonymous shell corporation.
Thus at the broadest level, of the 7,466 inquiries sent, the non-compliance level is 8.4 per cent, for an overall Dodgy Shopping Count of 12. The 8.4 per cent includes non-responses in the denominator, since conceivably some providers may fail to reply in response to risk and thus may be complying with international law in a ‘soft’ way. As a simplified measure, it is important to note that very high Dodgy Shopping Counts (ie, very low rates of non-compliance) in some cases exist alongside very high rates of compliance (eg, the Cayman Islands), very high rates of partial compliance (eg, Denmark), very high rates of refusal and non-response (eg, US law firms), or some combination of these. Thus, jurisdictions may have highly positive Dodgy Shopping Counts with very different patterns in the other categories.
Against the conventional policy wisdom, those selling shell companies from tax havens like the Cayman Islands, the Bahamas and Jersey were significantly more likely to comply with the rules than providers in OECD countries like Britain, Australia, Canada and especially the United States, which was one of the worst performers (see Tables 1 and 2). In the United States sample, the noncompliance level is 9.2 per cent and the Dodgy Shopping Count was 10.9, which was almost 10 per cent lower than the average in the international sample. Obtaining an anonymous shell company is therefore easier in the US than in the rest of the world.
Table 1: Dodgy Shopping Count by Country for Nations with at least 25 approaches. All Firms in none of the top eight countries were ever found noncompliant. Because there is no natural upper bound on the Dodgy Shopping Count, we set it to 100 for these.
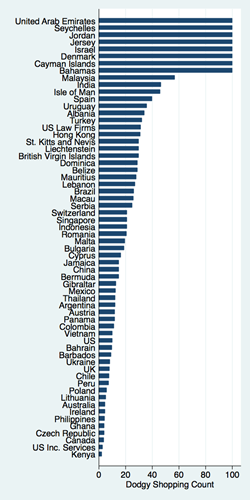
Figure 2: Dodgy Shopping Count by Type of Country Internationally and by Type of Firm in the United States
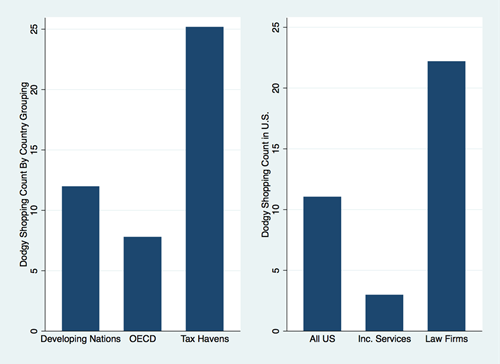
However, two factors worsen the gap between the US and other countries. First, the US number is elevated by the much higher non-response rate from firms in US sample, which was 77.3 per cent in the US compared to 49.3 per cent in the international sample. The proportion of providers in the US sample who replied to our inquiries and required no identity documents whatsoever was 41.5 per cent, which is roughly two-and-a-half times the average of 16.5 per cent in the international sample. We followed up with firms failing to reply to any of our emails with an innocuous inquiry basically asking if the firm was still in business and assisting customers but making no mention of confidentiality, taxes, or liability. We learned that the vast majority of non-responses are not soft refusals: they failed to respond to any inquiry, even the most innocuous that we could design. Only a tiny proportion of US providers of any kind met the international standard by requiring notarized identity documents (10 of 1722 in the US sample, less than one per cent). Thus our Dodgy Shopping Count measure tends to flatter the US by equating non-response with a form of compliance.
Another surprise was that providers in poorer, developing countries were at least as compliant with global corporate KYC standards as those in rich, developed nations. For developing countries the Dodgy Shopping Count is 12, while for developed countries it is 7.8. The significance of this finding is that it does not seem to be particularly expensive to enforce the rules on shell companies, given that poor nations do better than rich countries. This suggests that the relatively lacklustre performance in rich countries reflects a simple unwillingness to enforce the rules, rather than any incapacity. These results lend support to the results of a similar study by the World Bank, The Puppet Masters, which similarly concluded that rich, developed countries are generally the worst offenders in failing to meet corporate KYC standards.
Defying the international guidelines of a ‘risk-based approach’, shell company providers were often remarkably insensitive to even obvious criminal risks. Thus, although providers were less likely to reply to clear corruption risks than to approaches for low-risk profiles, those providers that did respond were also less likely to require certified identity documents of potential customers from high-corruption countries who claim to work in government procurement, a notoriously corruption-prone area.
Corporate service providers were significantly less likely to reply to potential terrorists and were also significantly less likely to offer anonymous shell companies to customers who are possibly linked to terror. However, compared to the low-risk baseline profile, a significantly lower share of firms replying to the terrorist profile refused service.
In some ways the biggest surprise was how little difference there was between the relatively innocuous low-corruption risk email and the obviously high-risk corruption approach, despite the international guidelines specifying that these customers should be subject to enhanced scrutiny. Excluding the US, the Dodgy Shopping Count was 11.5 for the low risk email, 11.3 for corruption, and 18.5 for terrorism financing risk. The results for the United States are 9 for the low risk email, 9.9 for corruption, and 17.4 for terrorism financing.
Varying the email approach to inform providers of the KYC rules they should be following made them no more likely to do so in the US or internationally, even when penalties for non-compliance were mentioned. The exception was in the US, where telling providers that the IRS enforced Know Your Customer standards reduced non-compliance (and thus increased the Dodgy Shopping Count from 9.5 to 13.2). In contrast, when customers offered to pay providers a premium to flout international rules, the rate of demand for certified identity documentation fell compared to the low-risk customer profiles.
These results represent by far the most detailed, extensive and reliable test of KYC rules in relation to shell companies ever performed, and the pattern that emerges as a result is worrying. Given the patchy overall level of compliance, the easy availability of formally prohibited untraceable shell companies, and the willingness of hundreds of businesses to supply obvious criminal risks with the corporate anonymity, the existing system seems to be very compromised. Many of these failings can be laid at the door of large, rich countries, especially the English-speaking OECD members and the United States above all, who conspicuously fail to apply standards that they have so energetically imposed on others.
[For full results of the study, please contact Jason Sharman at j.sharman@griffith.edu.au]
About the Author
Michael G Findley, Assistant Professor, University of Texas, Daniel L Nielson, Brigham Young University, and Jason Sharman, Centre for Governance and Public Policy, Griffith University